Build a resilient supply chain to preserve your value
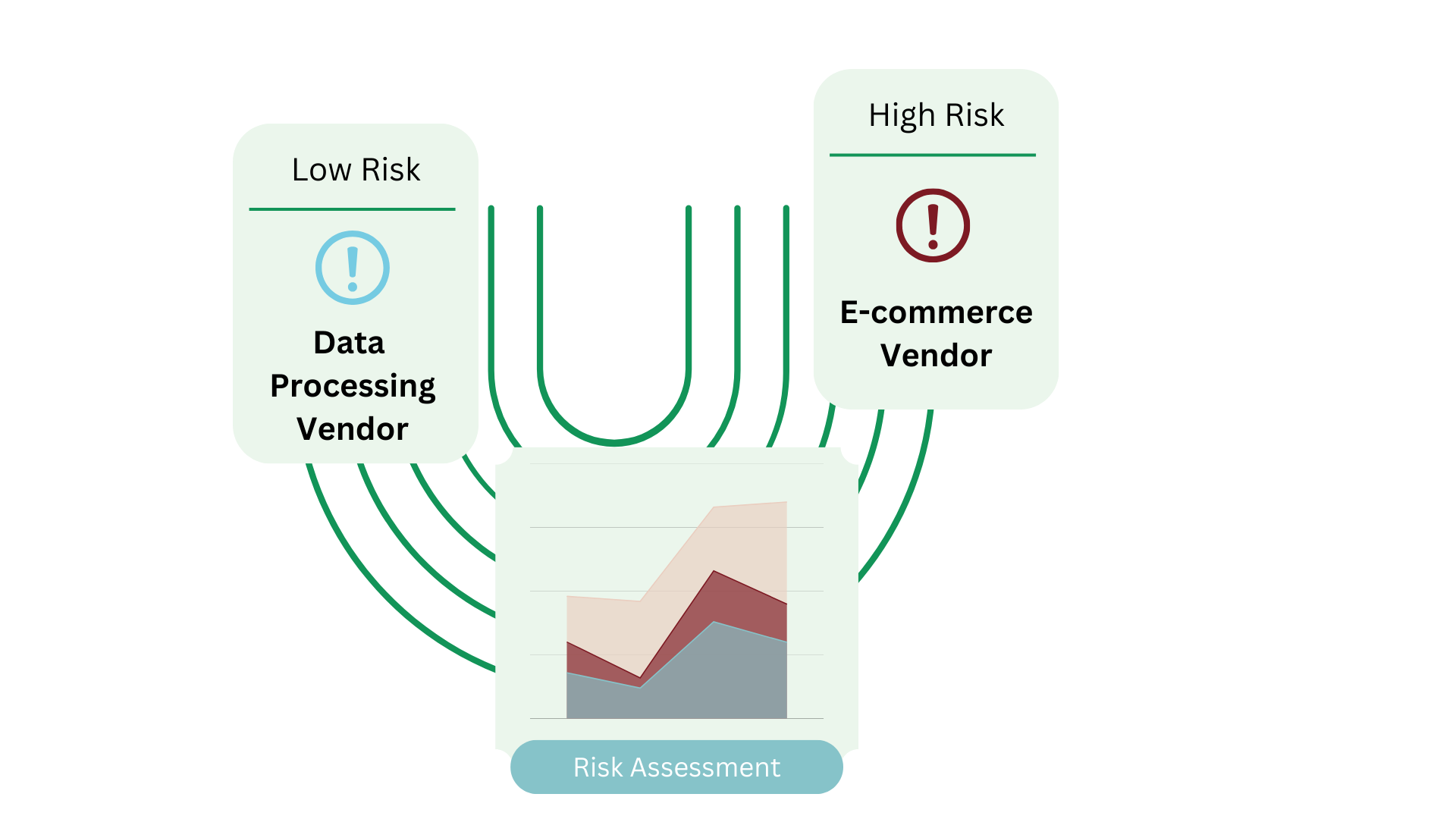
Second-party audit helps to assess and mitigate the information security risks posed by your suppliers and their compliance level – a confirmation of its suitability and compliance with your requirements set out in the contracts.

Certification Training
The training courses on The Certified Information Systems Auditor (CISA), Certified Information Security Manager (CISM), and Certified in Cybersecurity (CC) would help you prepare for the exams for these three of the most respected credentials in the cybersecurity industry
Learn more

Certification Consultation
Provide you with the preparation, establishment, and continual improvement of your privacy information management system to meet the demand of the ISO standards for managing information security risks, which can generally boost your internal energy as well as external reputation.
Learn more

Enterprise Risk Management
Assess and manage the existing and potential risks to the confidentiality, integrity, and availability of your information assets to help you achieve an acceptable risk level in operation
Learn more